Forgot these ugly limits for BIOS, DOS, FAT16 ... had to re-install a Siemens PCD-4ND
Sunday, November 25, 2012, 01:00 AM
Posted by Administrator
Yes, I am getting old. I forgot these days with ugly limits for harddisk access.
Not only logical limits (like FAT16 vs FAT32), also hardware limits.
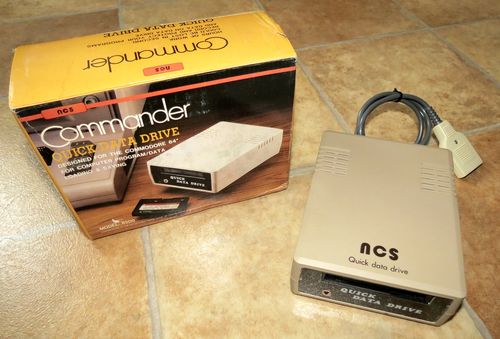
I have selled my Compaq Portable II last week, which was my floppy disk format conversion station (e.g. with such programs like Uniform, or 22Disk ...).
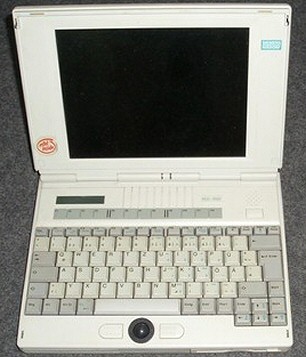
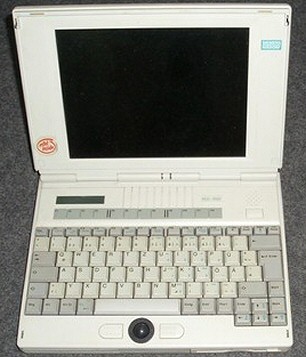
Now I took my PCD-4ND notebook, a very beautiful Intel 486 based old computer, which had a 500MB harddisk - way too small:
So I decided to exchange this 500MB IBM HDD with a newer Fujitsu 6.4GB HDD.
Guess what happened... I noticed a strange error message from my Windows 95 Setup, something like "harddisk size parameters are wrong, no LBA support".
I was a bit surprised because that Siemens PCD-4ND already had LBA support integrated in its Phoenix BIOS 1.03 from 1997.
But this LBA support was not really working, a Western Digital Tool "
DSKCHK" reported EXT INT13h Support is *NOT* supported by this most current available BIOS.
I tried Paragon Disk Manager 5.5, and tried to "fix" this wrong MBR / disk partition table.
It showed now 2GB free, but it still was not fixed for the Windows 95 Setup.
Without success I remembered there was a time special drivers were offered from Seagate or Maxtor (= Seagate Disk Manager or Maxblast).
It was a bit difficult to find an appropriate version of these tools, but after I formatted and installed
Disk Manager 9, it worked surprisingly without errors.
Think about how easy it is, to install new hardware and operating systems nowadays...
P.S.:
http://web.inter.nl.net/hcc/J.Steunebrink/bioslim.htm shows a lot of helpful information, but the embedded links are mostly NOT working anymore. I will try to create a similar webpage for my main site, but with current, working links. Be patient.






 Random Entry
Random Entry




